Chemical Plant Installation
Chemical plant installation is a complex and critical process that involves multidisciplinary engineering efforts, strategic planning, and strict adherence to...
Devamını Oku

Industrial automation systems form the backbone of modern infrastructure, enabling real-time monitoring and control of complex operational processes. From energy production facilities and oil refineries to manufacturing plants and water treatment systems, many critical operations rely on Supervisory Control and Data Acquisition platforms. These environments depend heavily on SCADA software to collect data from field devices, monitor system conditions, and allow operators to control industrial processes from centralized control rooms. As industries become more digital and interconnected, ensuring the security of these systems has become a top priority for organizations operating critical infrastructure.
Historically, SCADA systems were designed to operate in isolated networks with limited external connectivity. This architecture provided a natural layer of protection because the systems were not directly exposed to the internet or external networks. However, the industrial landscape has changed significantly over the last decade. Modern facilities increasingly integrate SCADA environments with enterprise IT systems, cloud platforms, remote monitoring services, and Industrial Internet of Things (IIoT) devices. While these integrations improve operational efficiency and data visibility, they also expand the potential attack surface for cyber threats.
In 2026, cybersecurity is no longer considered an optional enhancement for industrial environments; it is a fundamental requirement for operational reliability. Cyberattacks targeting industrial control systems have become more sophisticated, often aiming not only to steal data but also to disrupt physical operations. A successful breach can lead to production downtime, equipment damage, safety hazards, or even large-scale infrastructure disruptions. For industries such as energy, oil and gas, and utilities, these risks make SCADA cybersecurity a strategic priority.
Ensuring SCADA security requires a multi-layered defense strategy that combines technology, processes, and human awareness. Protective measures include network segmentation, secure authentication systems, continuous monitoring, vulnerability management, and incident response planning. Organizations must also adopt modern cybersecurity frameworks designed specifically for operational technology (OT) environments. When implemented effectively, these practices help protect industrial processes while maintaining the reliability and efficiency that SCADA systems are designed to deliver.
SCADA systems play a central role in managing and controlling industrial processes across many critical sectors, including energy, oil and gas, manufacturing, transportation, and water management. These systems collect real-time data from sensors, programmable logic controllers (PLCs), and field devices, enabling operators to monitor equipment performance and control industrial operations remotely. Because SCADA environments directly interact with physical processes, any disruption to these systems can have immediate operational consequences. For this reason, cybersecurity within SCADA infrastructures has become a fundamental component of industrial risk management in modern facilities.
One of the main reasons cybersecurity is critical in SCADA environments is the increasing integration between operational technology (OT) and traditional information technology (IT) networks. In the past, industrial control systems operated in isolated networks with limited connectivity. However, modern digital transformation initiatives have connected SCADA environments to enterprise networks, cloud platforms, and remote monitoring services. While this connectivity improves efficiency and decision-making capabilities, it also introduces new vulnerabilities. Attackers who gain access to corporate IT systems may attempt to move laterally into operational networks, potentially affecting industrial control processes.
Another important factor is the growing sophistication of cyber threats targeting industrial infrastructure. In recent years, ransomware groups and advanced persistent threat (APT) actors have increasingly targeted industrial control systems due to their strategic value. Instead of focusing solely on data theft, attackers now attempt to disrupt physical operations, manipulate control processes, or shut down production environments. Such incidents can result in significant financial losses, environmental risks, and safety hazards. As a result, organizations operating SCADA systems must implement proactive cybersecurity strategies that protect both digital assets and the physical infrastructure connected to them.
SCADA systems operate at the core of industrial automation environments, connecting field devices, control systems, and centralized monitoring platforms. Because these systems manage critical processes, they have become increasingly attractive targets for cyber attackers. Many industrial facilities still rely on legacy equipment and communication protocols that were not originally designed with cybersecurity in mind. As a result, vulnerabilities can emerge when these systems are connected to modern enterprise networks or remote monitoring infrastructures. Organizations must therefore understand the most common cyber risks associated with SCADA environments in order to implement effective protection strategies.
One major cybersecurity risk in SCADA systems stems from network exposure and insufficient segmentation between operational technology (OT) and information technology (IT) environments. When industrial control networks are directly connected to corporate networks without proper security controls, attackers can potentially move laterally from an IT system into the operational infrastructure. Once inside the SCADA environment, malicious actors may attempt to manipulate operational data, disrupt communications between controllers, or interfere with automated control processes. These types of attacks can significantly impact production continuity and system reliability.
Another key risk involves outdated software components and delayed security patching. Industrial systems are often designed for long-term operation, which means they may run for years without significant upgrades. While this ensures operational stability, it can also leave systems vulnerable to known security flaws. Attackers frequently exploit these unpatched vulnerabilities to gain unauthorized access or deploy malicious tools within industrial networks. To reduce this risk, organizations must implement structured vulnerability management programs that include regular updates, security testing, and proactive monitoring of industrial systems.
Unauthorized access is one of the most common cybersecurity threats affecting SCADA environments. Industrial control systems often involve multiple users, including operators, engineers, maintenance teams, and external service providers. If access permissions are not properly configured, attackers may exploit weak authentication mechanisms to gain entry into the system. In many legacy SCADA environments, default credentials, weak passwords, or shared user accounts still exist, significantly increasing the risk of unauthorized system access. Once attackers gain access to the control network, they may manipulate operational parameters, modify system configurations, or disrupt communication between controllers and monitoring stations.
Authentication vulnerabilities can also arise from poorly secured remote access channels. Industrial facilities frequently require remote connectivity for system maintenance, vendor support, or operational monitoring. If these connections are not properly protected through secure authentication protocols, attackers may exploit them as entry points into the industrial network. Implementing strong password policies, role-based access control (RBAC), and multi-factor authentication (MFA) significantly reduces the likelihood of unauthorized access. In addition, continuously monitoring user activity and logging access events allows organizations to detect suspicious behavior early and respond quickly to potential security incidents.
Malware specifically designed to target industrial environments has become a significant cybersecurity concern for organizations operating SCADA systems. Unlike traditional cyber threats that focus mainly on data theft, industrial malware is often designed to disrupt physical processes and operational technology environments. These attacks can infiltrate industrial networks through infected devices, compromised software updates, phishing campaigns, or unsecured remote connections. Once inside the network, malware can spread across systems, interfere with controller communications, or alter operational data displayed to system operators.
Industrial malware campaigns have evolved significantly in recent years. Advanced threats may target programmable logic controllers (PLCs), human-machine interfaces (HMIs), or data communication protocols used within SCADA infrastructures. Attackers may attempt to manipulate industrial processes, disable safety mechanisms, or cause production downtime. In some cases, malware is deployed as part of ransomware attacks, where cybercriminals encrypt critical operational systems and demand payment to restore access. These incidents can halt production lines and disrupt critical infrastructure operations.
To mitigate these risks, organizations must implement comprehensive cybersecurity strategies specifically designed for industrial environments. This includes deploying industrial-grade antivirus solutions, monitoring network traffic for anomalies, restricting external device usage, and regularly scanning systems for potential threats. Employee awareness training is also essential, as many attacks begin with human error such as opening malicious email attachments or downloading compromised files. By combining technology-based defenses with strong operational security practices, organizations can significantly reduce the likelihood of malware affecting their SCADA environments.
SCADA systems often contain security vulnerabilities that stem from legacy infrastructure, outdated communication protocols, and evolving connectivity requirements. Many industrial control systems were originally designed to prioritize reliability and operational stability rather than cybersecurity. As these systems become integrated with modern IT networks, cloud platforms, and remote access tools, previously isolated environments are exposed to new types of cyber threats. Without proper security controls, attackers may exploit weaknesses within the SCADA architecture to gain unauthorized access or disrupt industrial processes.
One of the most common vulnerabilities in SCADA environments is the use of outdated software and unsupported operating systems. Industrial equipment often remains in operation for many years, sometimes even decades, which means that software components may no longer receive security updates or vendor support. These outdated systems can contain known vulnerabilities that attackers can easily exploit. In addition, delayed patch management—often due to concerns about operational downtime—can leave systems exposed to publicly documented security flaws for extended periods.
Another frequently observed weakness involves poor network architecture and insufficient segmentation between industrial and corporate networks. When SCADA networks are directly connected to enterprise IT environments without adequate protection, attackers can move laterally between systems once they gain initial access. Other vulnerabilities may include weak access control policies, insecure communication protocols, and insufficient logging or monitoring capabilities. Addressing these issues requires organizations to perform regular security assessments, update system components when possible, and implement modern cybersecurity practices tailored specifically for operational technology environments.
Ensuring the security of SCADA systems requires a comprehensive approach that combines technical controls, operational policies, and continuous monitoring practices. Because industrial control systems directly influence physical processes, cybersecurity strategies must be carefully designed to avoid disrupting operational reliability. Modern SCADA security frameworks are built around the principle of layered protection, often referred to as “defense in depth.” This approach introduces multiple security layers across the network, system, and application levels, ensuring that if one layer is compromised, other protective mechanisms continue to defend the infrastructure.
One of the primary methods used to secure SCADA environments is implementing a well-structured network architecture. Industrial networks should be carefully separated from corporate IT networks through firewalls, secure gateways, and dedicated operational technology zones. This segmentation prevents attackers who compromise enterprise systems from easily accessing critical control infrastructure. Additionally, secure communication protocols and encrypted data transmissions are increasingly being adopted in modern SCADA deployments to protect sensitive operational data from interception or manipulation.
Another key method involves implementing strong access management policies and maintaining continuous system monitoring. Access to industrial systems should be restricted to authorized personnel only, with clearly defined user roles and permissions. Security monitoring platforms can analyze network traffic, detect abnormal activities, and generate alerts when suspicious behavior occurs. By combining secure network design, strict access control, vulnerability management, and real-time monitoring, organizations can significantly strengthen the overall cybersecurity posture of their SCADA environments.
Network segmentation is one of the most effective cybersecurity strategies used to protect SCADA environments. In industrial control systems, segmentation divides the network into separate zones that isolate critical operational components from less sensitive systems. By separating operational technology (OT) networks from corporate IT infrastructure, organizations significantly reduce the risk of attackers moving laterally across systems. This architecture ensures that even if a breach occurs within the enterprise network, attackers cannot easily access the industrial control environment. Segmentation is typically implemented using firewalls, secure gateways, and demilitarized zones (DMZs) that regulate communication between different network layers.
Security layers further strengthen this architecture by introducing multiple protective mechanisms across the system. These layers may include intrusion detection systems (IDS), intrusion prevention systems (IPS), secure remote access solutions, and industrial network monitoring platforms. Each layer provides an additional defense mechanism that helps detect or prevent malicious activity. In modern industrial cybersecurity strategies, layered security is critical because no single control can fully protect complex SCADA infrastructures. By combining segmentation with multiple security layers, organizations can significantly improve the resilience and protection of their industrial networks.
Strong authentication and authorization policies are essential components of SCADA cybersecurity. Industrial control systems typically involve multiple types of users, including operators, engineers, maintenance personnel, and external vendors who may require temporary system access. Without proper identity management, these environments can become vulnerable to unauthorized access and privilege misuse. Implementing structured access control policies ensures that users only have the permissions necessary to perform their specific roles. Role-Based Access Control (RBAC) is commonly used in industrial environments to restrict system privileges and reduce the risk of accidental or malicious changes to critical operational settings.
Modern SCADA environments increasingly rely on advanced authentication mechanisms to strengthen system security. Multi-factor authentication (MFA) has become an important defense layer, requiring users to verify their identity through multiple credentials such as passwords, authentication tokens, or biometric verification. In addition, organizations should implement centralized identity management systems that track and log user activity across the industrial network. Continuous auditing of user access, regular reviews of permission levels, and immediate revocation of unused accounts help maintain strict control over system access. These practices significantly reduce the likelihood of unauthorized system manipulation and improve overall industrial cybersecurity resilience.
Continuous monitoring and structured incident management are essential components of modern SCADA cybersecurity strategies. Because industrial control systems operate in real time and support critical infrastructure, detecting potential threats as early as possible is crucial. Monitoring systems collect data from network traffic, controllers, servers, and operator workstations to identify unusual behavior or anomalies. Advanced monitoring platforms such as Security Information and Event Management (SIEM) tools, industrial intrusion detection systems, and specialized OT security platforms analyze this data continuously to detect potential cyber threats. These systems allow organizations to identify suspicious activities before they escalate into operational disruptions.
Monitoring in SCADA environments also provides valuable insights into system performance and operational stability. By analyzing network behavior, device communications, and system logs, security teams can detect irregular patterns that may indicate cyber intrusions or system malfunctions. For example, unexpected changes in network traffic, unauthorized device connections, or abnormal command sequences may signal an attempted attack. In 2026, many industrial organizations are increasingly integrating artificial intelligence–driven monitoring tools that help detect subtle anomalies within large volumes of operational data. This allows security teams to respond more quickly and reduce the risk of prolonged system compromise.
Incident management complements monitoring by defining how organizations respond when a potential threat or security event is detected. A well-defined incident response plan outlines procedures for identifying the source of the attack, isolating affected systems, and restoring normal operations as quickly as possible. In industrial environments, incident response must be carefully coordinated to avoid interrupting critical processes or creating safety risks. After an incident is resolved, organizations typically conduct detailed post-incident analyses to understand the root cause and improve their security controls. This continuous improvement process helps strengthen SCADA security and prepares organizations to respond more effectively to future cyber threats.
SCADA security plays a crucial role in maintaining stable and efficient industrial operations. Industrial control systems are responsible for managing production lines, energy distribution networks, transportation infrastructure, and various automated processes that must operate continuously. Any disruption in these systems can lead to operational downtime, financial losses, and potential safety risks. By implementing strong cybersecurity measures, organizations can protect their operational environments from external threats while ensuring that critical processes continue to run smoothly.
Another important contribution of SCADA security is improved risk management across industrial operations. Cybersecurity frameworks designed for operational technology environments help organizations identify vulnerabilities before they are exploited. Through proactive monitoring, vulnerability assessments, and continuous security updates, companies can reduce the likelihood of cyber incidents affecting industrial processes. In addition, secure system architectures make it easier to detect abnormal behavior within industrial networks, allowing operators and security teams to respond quickly to potential threats.
SCADA security also supports compliance with international industrial cybersecurity standards and regulatory requirements. Many industries, especially those managing critical infrastructure such as energy, utilities, and transportation, must comply with strict security regulations. Implementing secure SCADA architectures helps organizations meet these compliance requirements while strengthening overall operational reliability. As industrial systems continue to evolve with digital transformation initiatives, integrating cybersecurity directly into operational technology environments will remain essential for protecting both physical infrastructure and digital assets.
SCADA systems are widely used to manage and operate critical infrastructure such as power generation facilities, oil and gas pipelines, water treatment plants, and transportation networks. Because these systems directly control physical processes, any cybersecurity breach can have consequences that extend far beyond digital systems. A successful attack on a SCADA environment could disrupt electricity distribution, interrupt fuel supply chains, or affect essential public services. For this reason, protecting SCADA systems is a key component of national and industrial cybersecurity strategies. Organizations responsible for critical infrastructure must therefore implement robust security measures that protect both digital networks and operational processes.
Protecting critical infrastructure requires a comprehensive security approach that includes network protection, strict access controls, continuous monitoring, and regular security assessments. Industrial organizations increasingly adopt international cybersecurity standards such as IEC 62443 and NIST guidelines to strengthen the resilience of operational technology environments. These frameworks provide structured security practices that help organizations manage cyber risks effectively. By implementing strong SCADA security strategies, organizations can safeguard essential services, maintain operational stability, and reduce the risk of large-scale disruptions affecting critical infrastructure.
Operational continuity is one of the most significant benefits of implementing strong SCADA cybersecurity practices. Industrial facilities depend on continuous system availability to maintain production efficiency, ensure safety, and meet operational targets. A cyber incident that disrupts SCADA systems can halt production lines, interrupt energy distribution, or delay essential industrial processes. Such disruptions can result in major financial losses and operational setbacks. By strengthening SCADA security frameworks, organizations can significantly reduce the risk of cyber incidents affecting their operational workflows and ensure that industrial processes remain stable and uninterrupted.
System resilience is closely linked to operational continuity and focuses on the ability of industrial systems to withstand disruptions and recover quickly from incidents. Modern SCADA architectures often incorporate redundancy mechanisms, data backup strategies, and disaster recovery plans to maintain system functionality even during unexpected failures. Regular system monitoring, proactive vulnerability management, and automated alerting systems also contribute to stronger resilience. When combined with well-defined incident response procedures, these measures enable organizations to detect problems early, isolate affected components, and restore normal operations with minimal downtime. By prioritizing both security and resilience, industrial organizations can maintain reliable and sustainable operations in an increasingly complex cybersecurity landscape.

Chemical plant installation is a complex and critical process that involves multidisciplinary engineering efforts, strategic planning, and strict adherence to...
Devamını Oku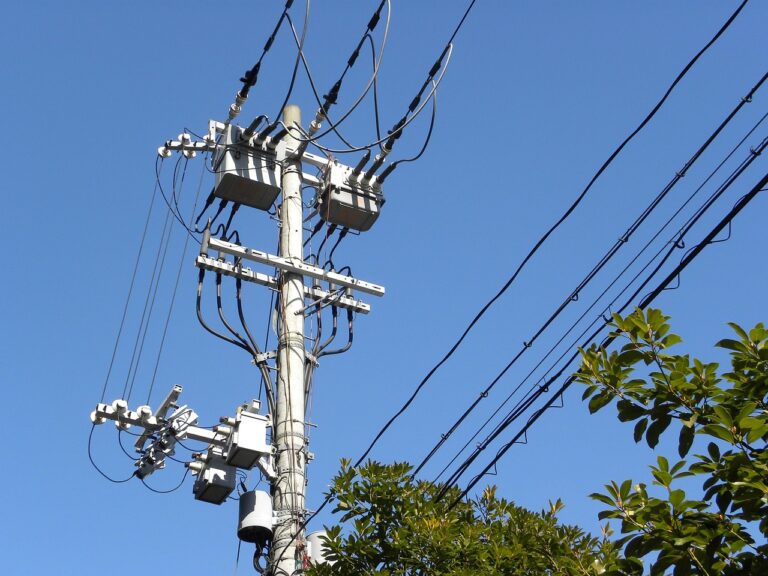
Efficient and secure energy transmission is only possible through the correct choice of a pole type transformer, which plays a...
Devamını Oku
Sustainable management of energy resources has become a strategic priority in today’s global landscape. In this context, underground gas storage...
Devamını OkuPROTECTION OF PERSONAL DATA
WEBSITE COOKIE POLICY
Your personal data; It is one of the leading principles of our Organization to protect the privacy of visitors to the website (www.adatech.com.tr) operated by ADATECH as the data controller. This Cookie Usage Policy (“Policy”) explains to all our website visitors and users which types of cookies are used and under what conditions.
Cookies are small text files stored on your device or network server by websites you visit on your computer or mobile device.
They are generally used to provide you with a personalized experience during your use of the website you visit, to improve the services offered and to improve your experience, and may contribute to ease of use while browsing a website. If you do not prefer the use of Cookies, you can delete or block Cookies in your browser settings. However, we would like to remind you that this may affect your use of our website. Unless you change your cookie settings in your browser, we will assume that you accept the use of cookies on this website.
1. WHAT KIND OF DATA IS PROCESSED IN COOKIES?
Cookies on websites, depending on their type, collect data about your browsing and usage preferences on the device you visit the site. This data includes information about the pages you access, the services and products you review, your preferred language option and other preferences.
2. WHAT is a solution and what are its intended uses?
Cookies are small text files that are stored on your device or network server through browsers by websites you visit. These small text files, which contain your preferred language and other settings on the site, help us remember your preferences the next time you visit the site and make improvements to our services to improve your experience on the site. Thus, you can have a better and personalized usage experience on your next visit.
The main purposes of using cookies on our Website are listed below:
3.TYPES OF COOKIES USED ON OUR WEBSITE
3.1. Oturum Çerezleri
Session cookies ensure that the website functions properly during your visit. They are used for purposes such as ensuring the security and continuity of our sites and you during your visit. Session cookies are temporary cookies, they are deleted when you close your browser and come to our site again, they are not permanent.
3.2. Persistent Cookies
These types of cookies are used to remember your preferences and are stored on your device via browsers. Persistent cookies remain stored even after you close your browser or restart your computer from which you visited our site. These cookies are kept in subfolders of your browser until they are deleted through your browser’s settings.
Some types of persistent cookies may be used to provide you with special suggestions, taking into account issues such as your purpose of using the Website.
Thanks to persistent cookies, if you visit our Website again with the same device, it is checked whether there is a cookie created by our Website on your device and if there is, it is understood that you have visited the site before and the content to be transmitted to you is determined accordingly and thus a better service is provided to you.
3.3. Mandatory/Technical Cookies
These cookies are essential for the website you visit to function properly. The purpose of such cookies is to provide necessary services by enabling the website to function. For example, it allows you to access secure parts of the website, to use its features, to navigate on it.
3.4. Analytical Cookies
They collect information about the way the website is used, the frequency and number of visits, and show how visitors navigate to the site. The purpose of using such cookies is to increase performance by improving the way the site functions and to determine the general trend direction. They do not contain data that could enable the identification of visitors. For example, they show the number of error messages displayed or the most visited pages.
3.5. Functional/Functional Cookies
It saves the choices made by the visitor within the site and remembers them on the next visit. The purpose of such cookies is to provide ease of use to visitors. For example, it prevents the site user from re-entering the user password on each page they visit.
3.6. Targeting/Advertising Cookies
They enable the measurement of the effectiveness of advertisements served to visitors and the calculation of the number of times the advertisements are viewed. The purpose of such cookies is to serve ads customized to the interests of visitors.
Likewise, they enable the detection of visitors’ interests specific to their browsing and the presentation of appropriate content. For example, it prevents the advertisement shown to the visitor from being shown again in a short time.
4. HOW TO MANAGE COOKIE PREFERENCES?
To change your preferences regarding the use of cookies or to block or delete cookies, simply change your browser settings.
Many browsers give you the option to accept or reject cookies, accept only certain types of cookies, or be alerted by the browser when a website requests to store cookies on your device so that you can control cookies.
It is also possible to delete cookies previously saved in your browser.
If you disable or refuse cookies, you may need to set some preferences manually, some features and services on the website may not function properly as we will not be able to recognize and associate your account. You can change the settings of your browser by clicking on the relevant link from the table below.
5. ENFORCEMENT OF WEBSITE PRIVACY POLICY
Website Privacy Policy …./…./…./…. . is dated. In case all or certain articles of the Policy are renewed, the effective date of the Policy will be updated. The Privacy Policy is published on the website of the Authority (www.adatech.com.tr) and made available to the relevant persons upon the request of the personal data owners.
ADATECH
Address: Esenyalı Neighborhood Yanyol Street Varyap Plaza No:61-148 Pendik / Istanbul
Telephone: +90 (216 ) 514 80 69
E-mail: info@adatech.com.tr
Web Address: www.adatech.com.tr